Buying a VPN in 2026:
A Beginner’s Guide
In 2026, with autonomous hackers, invasive ISPs, and algorithmic data brokers monitoring your every packet, a Virtual Private Network (VPN) is your foundational line of defense. This guide decodes the cryptographic jargon and shows you exactly how to deploy the perfect privacy shield.
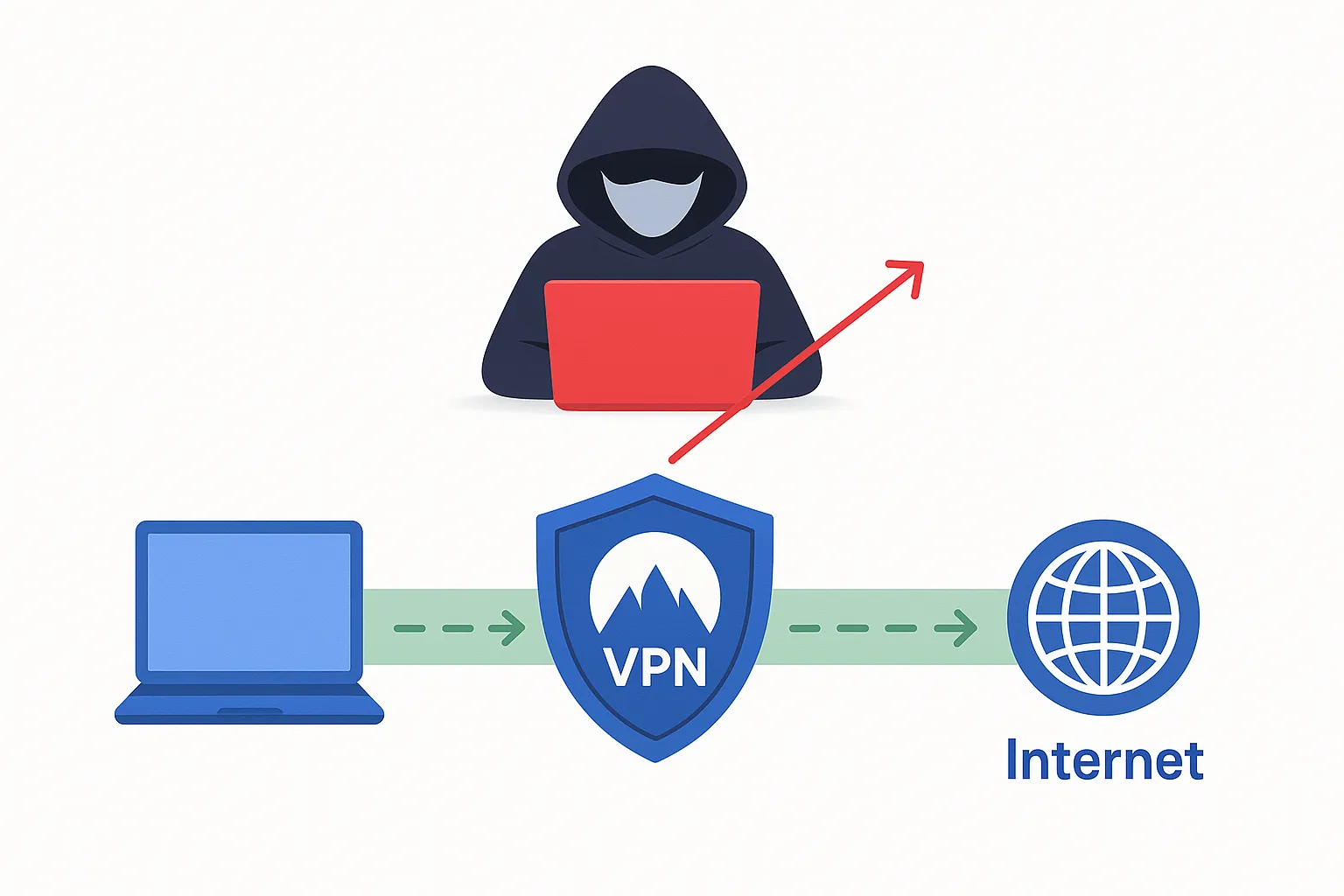
In short: A VPN (Virtual Private Network) is a cybersecurity tool that hides your real IP address and encrypts your internet traffic, preventing hackers, ISPs, and government agencies from tracking your online activity.
Why a VPN Matters in 2026
Our infrastructure is fully digitized. Over 1.6 billion people worldwide now deploy VPNs daily to secure their nodes. Here is exactly what the technology unlocks:
Network Hardening
Using public Wi-Fi broadcasts your data in plaintext. A VPN encrypts your traffic with AES-256 ciphers, turning your passwords and session cookies into unreadable static to packet-sniffers.
AI Profiling Defense
Corporate data brokers use AI to build highly predictive models of your behavior. A VPN masks your IP footprint, actively starving these algorithms of your personal data points.
IoT Ecosystem Shielding
Smart appliances and home networks are notoriously vulnerable. Routing your connection safeguards your entire hardware ecosystem from automated external intrusion.
Global Access Routing
VPNs act as geographic master keys. Connect to a foreign server to instantly bypass geo-blocks and unlock unrestricted streaming catalogs on platforms like Netflix and Hulu.
DDoS Mitigation
Gamers deploy VPNs to shield their residential IP addresses against targeted DDoS attacks, bypass ISP bandwidth throttling, and access region-locked competitive servers.
Censorship Evasion
An invaluable tool for remote operators. It secures corporate data on hotel networks and effortlessly punches through strict national firewalls when deployed abroad.
The Pros & Cons
The Advantages
-
Cryptographic Security: Wraps your data in unbreakable AES-256 encryption.
-
Zero Tracking: Leaves no digital trail; hides your IP from advertisers and ISPs.
-
DPI Bypass: Instantly circumvents Deep Packet Inspection and geo-blocks.
-
Data Autonomy: Reclaim absolute ownership of your digital footprint.
The Disadvantages
-
Overhead Latency: Rerouting and encrypting data can cause minor speed degradation.
-
Operational Costs: Trustworthy, audited networks require a premium subscription.
-
IP Blacklisting: Streaming sites actively try to block known VPN data center IPs.
-
Legal Status: Running encrypted nodes is strictly regulated in some authoritarian regions.
Jargon Decoder
VPN marketing relies heavily on complex technical terminology. Let’s translate the most critical protocols into plain English so you know exactly what architecture you are deploying.
🔐 Encryption (AES-256)
The cryptographic core of a VPN. AES-256 means the cipher is mathematically virtually unbreakable, ensuring interceptors see nothing but randomized static.
🕵️ RAM-Only Servers
Servers that run entirely on volatile memory rather than hard drives. Whenever the server is rebooted, all data is permanently and irreversibly wiped.
🛑 Kill Switch
An automatic emergency brake. If your VPN tunnel drops unexpectedly, it instantly severs your internet connection, preventing your real IP from leaking.
⚙️ Protocols (WireGuard)
The coded instructions building your tunnel. WireGuard is the modern standard, offering a hyper-efficient codebase that improves speeds without sacrificing security.
🔀 Split Tunneling
Allows you to route specific applications through the encrypted VPN while letting others connect directly to the local network (e.g., to use a wireless printer).
💧 DNS Leak Protection
Forces your DNS requests (the website URLs you type) to route through the secure tunnel, rather than bypassing it and alerting your ISP to your destination.
Critical Pitfalls to Avoid
The “Free VPN” Trap
If the network is free, you are the product. Free VPNs routinely monetize your traffic by logging and selling it to third parties. They also suffer from severe throttling. Never trust free infrastructure.
Unverified Logging Claims
Marketing copy saying “No Logs” is meaningless without proof. Only deploy VPNs that prove their zero-log architecture by passing regular, independent forensic audits by firms like Deloitte or PwC.
Operational Complacency
A VPN secures your network layer, but it does not make you immune to malware, ransomware, or phishing payloads. It is a critical security tool, but requires you to maintain strict personal OPSEC.
How to Choose the Right Architecture
🍿 For Global Streaming
Choose a provider engineered for rapid IP cycling to evade Netflix and Disney+ blocks. High bandwidth throughput is mandatory here to prevent 4K buffering.
⬇️ For P2P / Torrenting
Deploy a VPN that explicitly supports P2P traffic on dedicated nodes. An audited no-logs policy and a reliable Kill Switch are absolutely mandatory for anonymous transfers.
💼 For Remote Enterprise
If accessing corporate networks, prioritize dedicated IPs and advanced split-tunneling. This routes sensitive Jira/AWS traffic securely while keeping personal browsing local.
🌍 For Deep Censorship
Operating in highly restricted regions (like China or Iran) requires obfuscated servers. This masks the cryptographic handshake, hiding the fact that you are running a VPN protocol at all.
🕵️ For Absolute OPSEC
Journalists and activists require extreme anonymity. Demand RAM-only infrastructure, Double-VPN (MultiHop) routing, and Tor-over-VPN compatibility to ensure forensic tracking is mathematically impossible.
🕹️ For Competitive Gaming
Focus on providers boasting massive global server fleets to minimize packet travel distance. Look for localized nodes that offer native anti-DDoS shielding to protect your matches.
Top VPN Infrastructures of 2026
To optimize your deployment, these are the three undisputed industry leaders. They feature iron-clad algorithms, strict zero-log policies, and 30-day money-back guarantees.
NordVPN
Operating out of privacy-friendly Panama, NordVPN excels with advanced cryptography, Double VPN routing, and built-in malware blocking for elite OPSEC.
ExpressVPN
Engineered for hyper-fast connection protocols and a massive network spanning 100+ countries. The premier choice for consistently bypassing streaming geo-blocks.
Surfshark
An elite budget option that does not bottleneck performance. Surfshark allows unlimited simultaneous connections to secure massive, multi-device hardware ecosystems.
Frequently Asked Questions
Are free VPNs safe to use?
No. If a VPN network is free, you are the product. Free VPNs routinely monetize your traffic by logging and selling your data to third-party brokers, and they often suffer from severe bandwidth throttling.
What is a VPN Kill Switch?
A VPN Kill Switch is an automatic emergency brake. If your secure VPN tunnel drops unexpectedly, the kill switch instantly severs your internet connection to prevent your real IP address from leaking to your ISP.
What are RAM-Only VPN servers?
RAM-only servers run entirely on volatile memory rather than traditional hard drives. This means that whenever the VPN server is rebooted, all user data and routing history is permanently and irreversibly wiped.
Does a VPN stop ISP tracking?
Yes. A VPN wraps your internet data in AES-256 encryption before it leaves your device. Your ISP can see that you are connected to a VPN, but they cannot see the websites you visit or the data you transmit.
About the Author
Andreas Lazarou is the Lead Security Engineer at VPNDeals. With over a decade of experience in cryptographic protocols and network architecture, he specializes in identifying vulnerabilities in routing infrastructure, testing zero-log environments, and auditing enterprise firewall deployments.
Deploy Your Security Layer Today
A VPN is no longer reserved for sysadmins; it is a foundational necessity for anyone operating on the modern web. Take the first step toward absolute data autonomy today.

